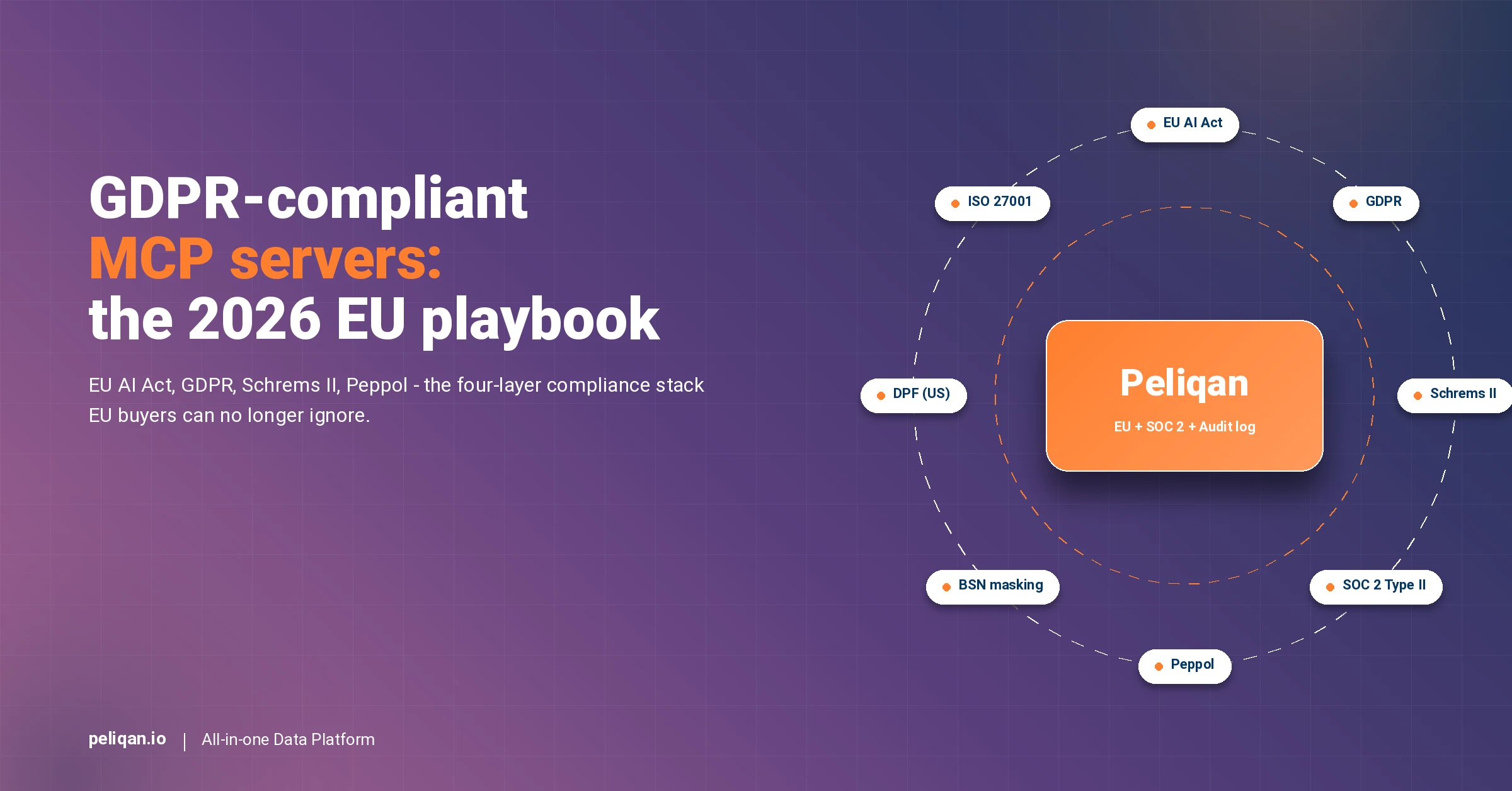
The EU AI Act entered force on August 1, 2024. Article 5 prohibitions kicked in on February 2, 2025. General-purpose AI obligations began on August 2, 2025. Furthermore, the full high-risk AI system requirements become enforceable on August 2, 2026 – with fines of €35M or 7% of global turnover for the most serious violations. Meanwhile, GDPR fines continue at €20M or 4% of turnover, and the Belgian Peppol mandate added €1,500-€5,000 fines for non-compliant B2B invoices starting January 1, 2026.
However, most MCP servers on the market today were not built for this compliance stack. Composio, Pipedream, Zapier MCP, Apideck, CData, Stackone – the leading platforms are US-hosted by default, with EU support added later (if at all). Apideck’s May 13, 2026 Product Hunt launch positioned the product on “200+ apps” with no specific EU compliance framing.
Consequently, EU buyers face a real architectural question in 2026: which MCP servers actually survive a SOC 2 audit, an EU AI Act review, and a CNIL or AP inquiry? This blog is the answer.
The post covers the 2026 compliance stack, the seven things a gdpr-compliant mcp server actually needs, the four questions every EU buyer should ask any vendor, a head-to-head comparison of seven leading MCPs, the EU AI Act risk classification for MCP-based AI agents, and an industry-by-industry decision framework. It is the platform-level reference for CIOs, CDOs, CISOs, and compliance officers building AI strategy under EU regulation in 2026.
Why the 2026 compliance stack changes everything for MCP
Three regulatory layers converged on EU AI buyers in early 2026. Firstly, the EU AI Act is now actively enforced, with the highest-tier prohibitions live since February 2025 and the high-risk system obligations landing in August 2026. Per the European Commission’s regulatory framework, the full applicability date is the most critical milestone for the majority of EU buyers. Secondly, GDPR remains the baseline with continued enforcement: CNIL alone issued €486M in fines in 2025, including €150M against SHEIN and €50M against Orange. Thirdly, sector-specific mandates like Belgium’s Peppol e-invoicing rule add another compliance dimension that AI agents touching invoice data must respect.
Specifically, MCP servers sit in the middle of this stack. The MCP layer is what AI clients (Claude, ChatGPT, Cursor) use to read and write into business systems. Therefore, the data residency, audit logging, and access-control posture of the MCP determine whether the entire AI workflow is defensible.
Why the question is structural, not vendor-specific
Most MCP buying conversations in 2025 focused on app catalog breadth and OAuth ergonomics. In 2026, those questions are still important. However, they are downstream of the bigger architectural decision: is the MCP hosted in EU jurisdiction, does it log every prompt-to-API mutation, and does it satisfy the EU AI Act risk classification for the data it touches?
Getting these wrong has compounding costs – a SOC 2 audit failure, a CNIL fine, an EU AI Act enforcement action, or a public-sector procurement disqualification. Conversely, getting them right unlocks the EU enterprise and government segments that US-default MCPs cannot serve.
The 2026 EU compliance stack: four regulations every MCP must respect
The four regulatory layers shaping EU MCP choice in 2026
Why MCP servers are squarely inside this scope
MCP servers process customer data, employee data, financial data, and operational data on behalf of AI agents. As such, an MCP that handles EU resident data is a data processor under GDPR. Additionally, when the MCP enables an AI agent that produces decisions affecting EU citizens (lead scoring, risk classification, automated finance actions), the EU AI Act risk classification can apply.
Consequently, an MCP buying decision is now a compliance decision. The vendor’s hosting jurisdiction, audit logging, sub-processor list, and DPA terms matter as much as the connector catalog or the price.
What a GDPR-compliant MCP server actually needs
The seven structural requirements EU buyers must verify
How these seven requirements compound
Each requirement closes one specific exposure. Together, they form the documented compliance posture that lets a CIO sign off on an AI strategy without inheriting unbounded regulatory risk. By contrast, missing even one – especially data residency or audit log – creates a structural gap that no feature parity from a US-default platform can close.
The 4 questions EU buyers must ask any MCP vendor
The procurement checklist for EU MCP buyers in 2026
Head-to-head: 7 MCP platforms on EU compliance posture
Reading the comparison fairly
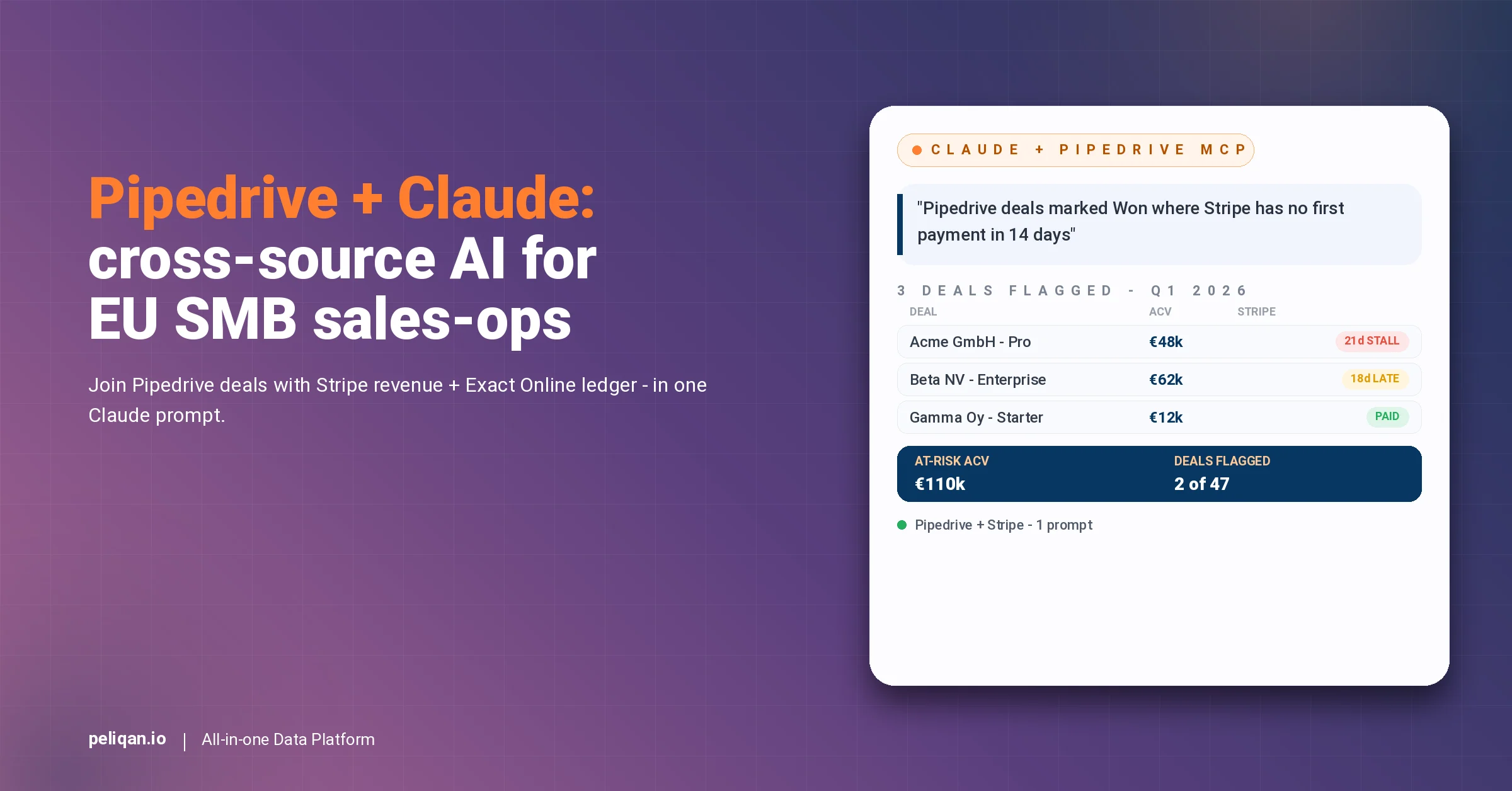
Composio and Pipedream are strong platforms with mature SOC 2 posture. However, their US-default hosting means EU buyers fall back on SCCs and the DPF for transfers – a defensible but fragile position. By contrast, Peliqan is EU-headquartered with EU-hosted infrastructure as the structural default.
Additionally, the vertical depth column matters more than EU buyers initially think. An MCP that ships native depth into Yuki, Silverfin, Billit, Exact Online, AFAS, and Teamleader is one that understands the Belgian and Dutch SMB stack – and that depth correlates with the compliance posture serious EU buyers need.
The EU AI Act risk classification for MCP-based AI agents
The EU AI Act sorts AI systems into four risk tiers: unacceptable (prohibited), high-risk, limited-risk, and minimal-risk. Specifically, most business-data MCP workflows fall into the limited-risk or minimal-risk tiers. However, certain use cases trigger the high-risk obligations that become enforceable in August 2026.
Which MCP workflows are high-risk under the AI Act
Firstly, AI agents that make decisions affecting natural persons in employment contexts (hiring, performance review, dismissal recommendations) are high-risk under Annex III. Consequently, an MCP wired to a CRM that scores candidate fit or routes employees automatically falls into scope.
Secondly, AI agents that perform credit scoring or financial risk decisioning are high-risk. By extension, AI workflows that auto-approve invoices, set credit limits, or flag transactions for AML review need the documentation, transparency, and human-oversight obligations of high-risk systems.
Thirdly, AI agents that process biometric data or operate in critical infrastructure are high-risk by category. These cases are rare for typical business-data MCPs but should be classified explicitly.
What limited-risk MCP workflows still require
Most CRM, ERP, accounting, and operational AI workflows are limited-risk – which still triggers transparency obligations (users must know they are interacting with AI) and the broader GDPR baseline. Naturally, the audit log requirement applies regardless of risk tier when the AI agent touches personal data.
Decision framework: which MCP posture fits your industry
Match the MCP compliance posture to your sector
Peliqan’s compliance footprint: how the platform answers the four questions
Peliqan’s documented compliance posture
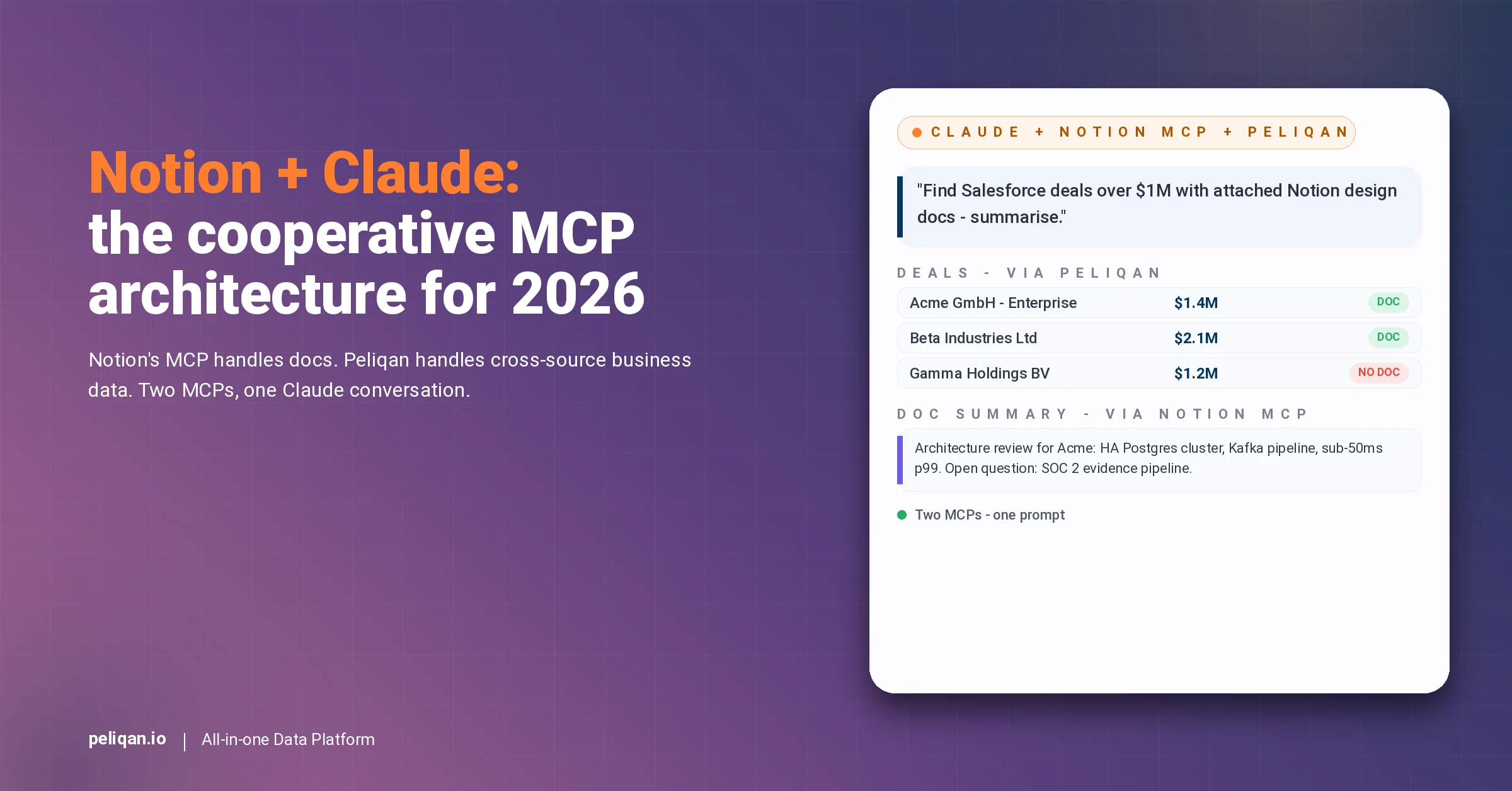
Why the architecture choice compounds across the cluster
Specifically, an EU buyer adopting Peliqan for one vertical (say, Exact Online for finance) inherits the same compliance posture across every other connector in the platform. As a result, when the same buyer extends to Salesforce, Stripe, or MEWS, the EU hosting, SOC 2 posture, and audit log apply uniformly.
Furthermore, the main MCP hub covers the cross-source architecture and the ROI math for a typical EU mid-market group.
Additionally, the general Claude MCP overview explains how Anthropic’s protocol works end-to-end with EU-compliant LLM providers, plus the architectural pattern that decouples the data layer from the AI provider.
Pairing Peliqan with a GDPR-compliant LLM
The compliance posture of the MCP layer matters most when paired with an LLM that has matching residency and DPA terms. Anthropic’s Claude offers enterprise tiers with EU residency. Likewise, OpenAI Enterprise, Mistral, and self-hosted open models like Llama 3 give EU buyers compliant inference options.
Importantly, the MCP architecture decouples the data layer from the AI provider. Therefore, a switch from one LLM to another does not require re-architecting the MCP – the compliance posture of the platform layer remains stable.
The implementation primitives that make compliance enforceable
Compliance posture on the website is not enough. Importantly, the architecture has to enforce the controls at the data layer. Specifically, three Peliqan implementation primitives turn the compliance posture from a checklist into an operational reality.
Permissions at source, dataset, column, and action level
Peliqan’s permissions documentation covers the role-based access model. Specifically, the DPO and the security team can grant access at four levels: the source (which connector), the dataset (which table), the column (which fields), and the action (read vs write). This granularity is what makes BSN masking, salary protection, and audit-grade access control enforceable rather than aspirational.
Audit-logged reverse ETL for writeback
Reverse ETL in Peliqan is the writeback engine. Naturally, every mutation through reverse ETL records the originating prompt, the authorising user, the source data, and the destination API response. As a result, the audit trail is the same trail a SOC 2 auditor or an EU AI Act assessor will ask for.
Data quality monitoring with alerting
Furthermore, data quality monitoring handles the proactive layer. Specifically, anomaly detection on PII access patterns, unusual writeback frequency, or out-of-policy data movement can trigger Slack or email alerts to the DPO before issues compound. This is exactly the kind of operational signal that turns audit readiness into ongoing operational discipline.
What CIOs, CISOs, and DPOs should do this quarter
Three concrete steps turn the EU AI Act + GDPR + Peppol compliance landscape from a worry list into a defensible 2026 posture.
Firstly, audit every MCP server currently in production for EU hosting jurisdiction, SOC 2 Type II status, audit log retention, and the documented sub-processor list. Any tool failing two or more of these four checks should be on a replacement timeline before the August 2, 2026 EU AI Act high-risk obligations land.
Secondly, classify each MCP-driven AI workflow against the EU AI Act risk tiers. Most business-data workflows are limited-risk and need only transparency plus baseline GDPR. However, HR decisioning, credit scoring, biometric data, and critical infrastructure require high-risk documentation, human oversight, and the August 2026 readiness window.
Thirdly, formalise the four-question procurement checklist (data residency, audit log, sub-processor list, AI Act classification) into your standard vendor evaluation flow. Specifically, any MCP vendor that cannot answer all four cleanly should be escalated to security review before procurement signs.
Ultimately, the EU buyers who win the next two years are those who treat MCP compliance as architecture, not afterthought. By contrast, the buyers who pick US-default platforms today will face migration costs and audit findings during the same enforcement windows that will define the EU AI market for the rest of the decade.